Electronic Reuse and Data Sanitization - Safeguarding Customer Trust and Fostering Business Growth through Robust Data Security
- Jan 19, 2024
- 3 min read
Technological innovation in the way of consumer electronics devices is moving so rapidly at this time it’s hard to keep up. The is innovation is coupled with electronic devices becoming more and more convenient and intuitive to use. With the increasing integration of smart devices into our everyday day life these devices are storing more and more personal, private, sensitive information or data.
As more and more electronic devices phase out and are no longer marketable all of these data containing devices with individuals personal and private details: pictures, messages and conversations, medical and financial records, just to name a few potential data leak risks, could be comprised and obtained by people interested in capitalizing off of your information. The risk is high and a very and present danger. One might pose the questions:
How can one be assured that their data is being effectively managed, wiped, and permanently destroyed?
Resellers, Refurbishers, and Recyclers
Customer trust is paramount! For organizations that work with used electronic data containing media, devices, and components customer trust is crucial for businesses striving to achieve sustainable growth. The critical elements of this trust center around the responsible handling of sensitive data. Ensuring that customer data and information is secure and effectively managed and destroyed so that no data breaches or leaks occur.
The security of customer information, data and the protection of their privacy is not only an ethical responsibility of these organizations but also aligned with the strategic business strategy for business growth.
One of the most effective strategies for effectively controlling data security and sanitization risks is to implement a certified management system and/or performance standard. There are several international standards available that address data sanitization and security best practices. Several of these standards are integrated with quality, environmental, health and safety to ensure the organization has all bases covered when working with potential hazardous used electronic devices.
The used electronics recycling standards:
R2v3 – Reuse and Recycling
RIOS – Recycling Industry Operating Standard
e-Stewards –Stewards of Excellence in Ethical Electronics Recycling and Reuse
These standards have requirements for managing data containing media and devices to ensure effective data sanitization both logical sanitization and physical destruction methods. Certification to one of these standards is evidence that the organization has compiled to these data security and sanitization requirements.
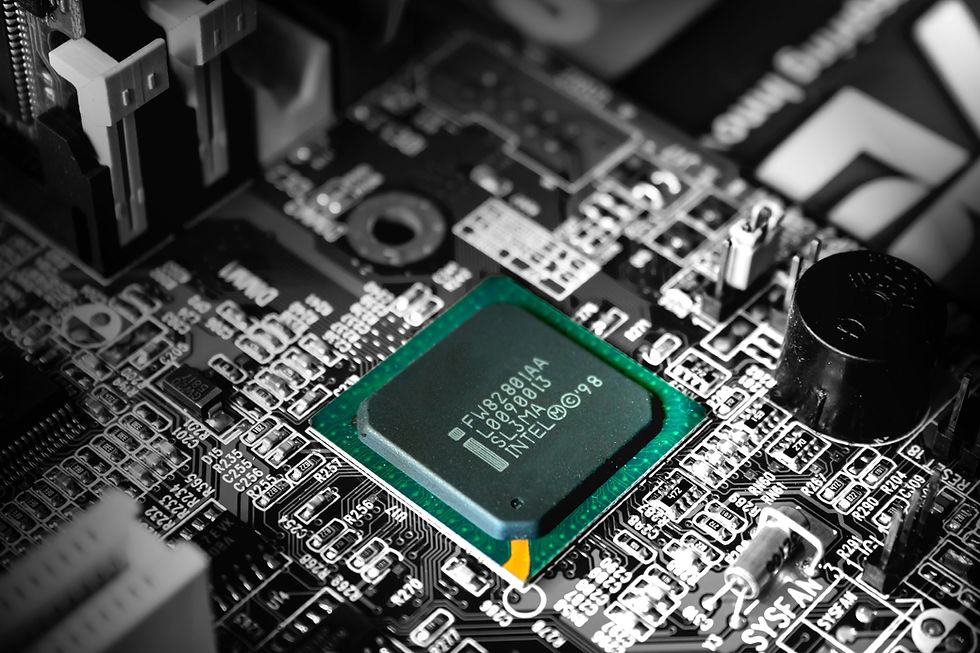
Understanding Data-Containing Devices
Various devices will be accepted by a recycler have the potential to store sensitive data. These include:
· Computers and Laptops: Primary repositories of business and customer data.
· Smartphones and Tablets: Mobile devices often hold sensitive information, especially with the increasing use of mobile apps.
· Mobile Phones
· Smart Watches and Wearables
· Smart TVs and Smart Appliances
· Point of Sales (POS) devices
· External Drives and USBs: Used for data transfer, these devices may carry critical business data.
· Printers and Photocopiers: Often overlooked, these devices can store copies of documents.
· Servers and Network Equipment: Central hubs for data storage and processing.
Types of Data-Containing Media
Understanding the types of media that store data is crucial for effective data security. This includes:
· Hard Drives (HDDs and SSDs). Commonly used in computers and servers.
· Solid State Drives (SSDs): Faster and more durable alternatives to traditional hard drives.
· Flash Drives and Memory Cards: Portable storage solutions often used in various devices.
· Printers and Copiers: May retain copies of printed or scanned documents.
Methods of Destruction and Sanitization
To mitigate the risk of data breaches, businesses should adopt thorough data destruction and sanitization methods. This involves both logical and physical destruction:
Logical Destruction:
Data Wiping: Overwriting stored data to make it irretrievable.
Encryption: Protecting data through advanced encryption methods.
Physical Destruction:
Shredding: Breaking down physical media into smaller, irrecoverable pieces.
Degaussing: Using powerful magnetic fields to erase data from magnetic media.
Best Practices for Data Security
Implementing a comprehensive data security strategy involves adopting best practices:
· Regular Audits: Conduct regular audits to identify and assess potential vulnerabilities.
· Employee Training: Educate employees on data security protocols and the importance of responsible data handling.
· Secure Disposal Policies: Establish clear policies for the disposal of devices and media containing sensitive information.
Prioritizing data security not only safeguards customer trust but also lays the foundation for sustainable business growth. By understanding the devices and media that may contain sensitive data and implementing robust destruction and sanitization methods, businesses can fortify their defenses against data breaches and ensure a secure digital environment. In an era where data is a valuable asset, protecting it becomes integral to both ethical business practices and long-term success.
Find out more on how the R2v3, RIOS or e-Stewards standard implementation and certification to these standards.
#Seri#R2v3Standard#Electronicrecyclers#Reuse#Ewaste#R2wilkshireConsulting#consulting#Management#sustainability#healthandsafety#environmental#training



























Comments